We turn information into anticipation
We provide visibility into external threats and potential data leaks that could affect your organisation. Through continuous monitoring of open and non-visible sources, we anticipate risks and enable a proactive response.
Brand and Domain Protection
We monitor the misuse of your brand and domains to detect impersonation and fraud attempts. In doing so, we help preserve your brand’s reputation and customer trust.
We detect brand impersonation, identify domains that mimic the organisation, and prevent the spread of fake websites and cloned profiles. In doing so, we reduce the risk of fraud to customers and employees and protect the trust and credibility of the organisation.
We implement a process for detecting, identifying, monitoring, and tracking the Dark Web and Deep Web, which allows us to assess and analyse any latent threats in illegal forums in order to prevent them in advance.
- Reduction of the risk of fraud and impersonation.
- Obtaining a comprehensive analysis of potential threats to the company.
- Taking early action against possible attacks on the reputation and image of our brand and domain.

Continuous Dark Web and Deep Web Monitoring
We continuously track the Dark Web and Deep Web to uncover leaked data, compromised credentials or emerging threats — enabling you to respond before any damage occurs.
We provide a service to identify threats against your company on the Dark Web and Deep Web. This includes identifying exposed corporate information, leaked credentials, classified information, etc. This information poses a serious threat that must be detected and resolved.
We use tools to monitor, detect and identify the leakage and exposure of sensitive information, as well as credentials and passwords that could be used for future attacks. This monitoring allows us to anticipate potential campaigns and threats that may arise.
- Strategic advantage in detecting and preventing potential threats.
- Early detection and identification of information leaks and exposed credentials allows us to anticipate future attacks.
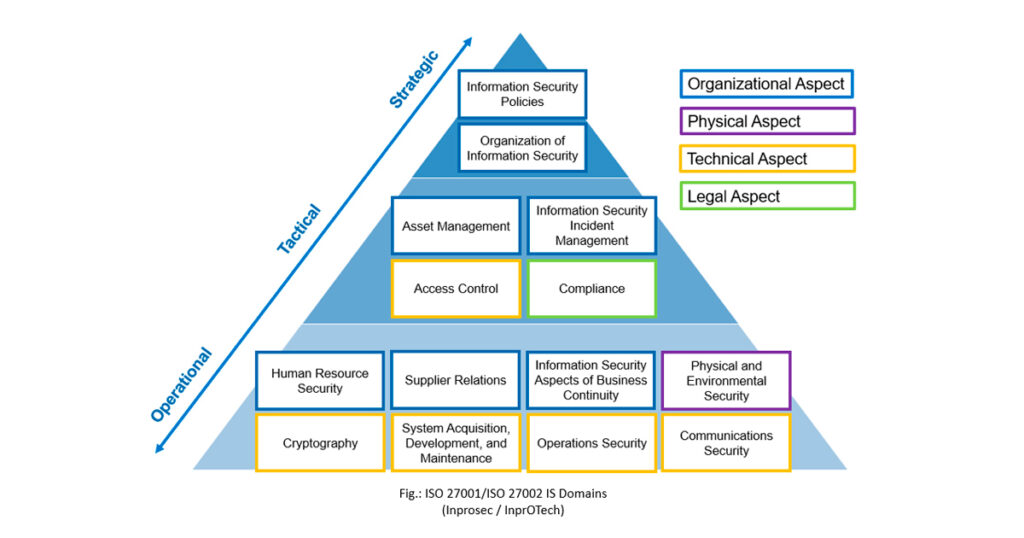
- Regulatory compliance with proactive threat management and cyber threat intelligence (ENS, ISO 27001 and NIST CSF).